From early days of online stores:
Getting a 90% discount by entering .1 in the quantity field of the shopping cart. The software properly calculated the total cost as .1 * cost, and the human packing the order simply glossed over the odd "." in front of the quantity to pack :)
The least forgivable security hole, and unfortunately a very common and easy to find one at that, is Google hacking. Case in point:
http://www.google.com/search?q=inurl%3Aselect+inurl%3A%2520+inurl%3Afrom+inurl%3Awhere
It's amazing how many pages on the Internet, government sites in particular, pass an SQL query through the query string. It's the worst form of SQL injection, and it takes no effort at all to find vulnerable sites.
With minor tweaks, I've been able to find unprotected installations of phpMyAdmin, unprotected installations of MySQL, query strings containing usernames and passwords, etc.
Social Engineering:
<Cthon98> hey, if you type in your pw, it will show as stars
<Cthon98> ********* see!
<AzureDiamond> hunter2
<AzureDiamond> doesnt look like stars to me
<Cthon98> <AzureDiamond> *******
<Cthon98> thats what I see
<AzureDiamond> oh, really?
<Cthon98> Absolutely
<AzureDiamond> you can go hunter2 my hunter2-ing hunter2
<AzureDiamond> haha, does that look funny to you?
<Cthon98> lol, yes. See, when YOU type hunter2, it shows to us as *******
<AzureDiamond> thats neat, I didnt know IRC did that
<Cthon98> yep, no matter how many times you type hunter2, it will show to us as *******
<AzureDiamond> awesome!
<AzureDiamond> wait, how do you know my pw?
<Cthon98> er, I just copy pasted YOUR ******'s and it appears to YOU as hunter2 cause its your pw
<AzureDiamond> oh, ok.
From bash.org
True story from my early days at Microsoft.
You haven't known fear until the day you wake up and see the headline on ZDNet.com that morning is "Worst Internet Explorer Security Hole Ever Has Been Discovered In 'Blah'" where 'Blah' is code you wrote yourself six months previously.
Immediately upon getting to work I checked the change logs and discovered that someone on another team -- someone we trusted to make changes to the product -- had checked out my code, changed a bunch of the security registry key settings for no good reason, checked it back in, and never got a code review or told anyone about it. To this day I have no idea what on earth he thought he was doing; he left the company shortly thereafter. (Of his own accord.)
(UPDATE: A few responses to issues raised in the comments:
First, note that I choose to take the charitable position that the security key changes were unintentional and based on carelessness or unfamiliarity, rather than malice. I have no evidence one way or the other, and believe that it is wise to attribute mistakes to human fallibility.
Second, our checkin systems are much, much stronger now than they were twelve years ago. For example, it is now not possible to check in code without the checkin system emailing the change list to interested parties. In particular, changes made late in the ship cycle have a lot of "process" around them which ensures that the right changes are being made to ensure the stability and security of the product.)
Anyway, the bug was that an object which was NOT safe to be used from Internet Explorer had been accidentally released as being marked "safe for scripting". The object was capable of writing binary files -- OLE Automation type libraries, in fact -- to arbitrary disk locations. This meant that an attacker could craft a type library that contained certain strings of hostile code, save it to a path that was a known executable location, give it the extension of something that would cause a script to run, and hope that somehow the user would accidentally run the code. I do not know of any successful "real world" attacks that used this vulnerability, but it was possible to craft a working exploit with it.
We shipped a patch pretty darn quickly for that one, let me tell you.
I caused and subsequently fixed many more security holes in JScript, but none of them ever got anywhere near the publicity that one did.
I hope you can spot what's wrong here. (Terribly wrong, in fact):
String emailBody = "";
for (int i = 0; i < subscribers.Count; i++)
{
emailBody += "Hello " + subscribers[i].FirstName + ",";
emailBody += "this is a reminder with your account information: \n\n:";
emailBody += "Your username: " + subscribers[i].Username + "\n";
emailBody += "Your password: " + subscribers[i].Password + "\n";
emailBody += "Have a great day!";
emailDispatcher.Send(subscribers[i].EmailAddress, emailBody);
}
The last recipient was the happiest ;)
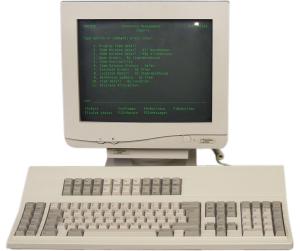
The old IBM System 36 dumb terminals had a keyboard combination that started the recording of a macro. So when a terminal was not logged in, you could start the recording of a macro and leave it in that position. Next time someone logged in, the keystrokes would be recorded in the macro and the recording would end automatically when maximum allowed keys was recorded. Just come back later and replay the macro to autolog-in.
If you love us? You can donate to us via Paypal or buy me a coffee so we can maintain and grow! Thank you!
Donate Us With